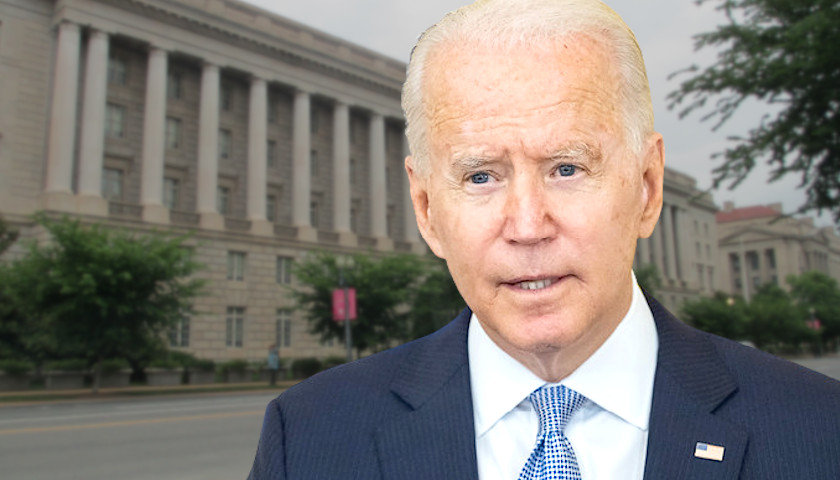
The Biden administration announced Thursday it will investigate Chinese-made “smart cars,” citing national security risks and surveillance concerns.
The investigation will center around concerns that Beijing could use Chinese smart cars inside the U.S. to collect information on the driver and the area surrounding the vehicle, according to the White House. U.S. intelligence agencies have warned that China has capabilities allowing it access to a score of key infrastructure systems, which could potentially be exploited in the event of a global emergency.
Read More